Defense In Depth Cybersecurity Solutions
Comprehensive Security Architecture Designed for Resilience
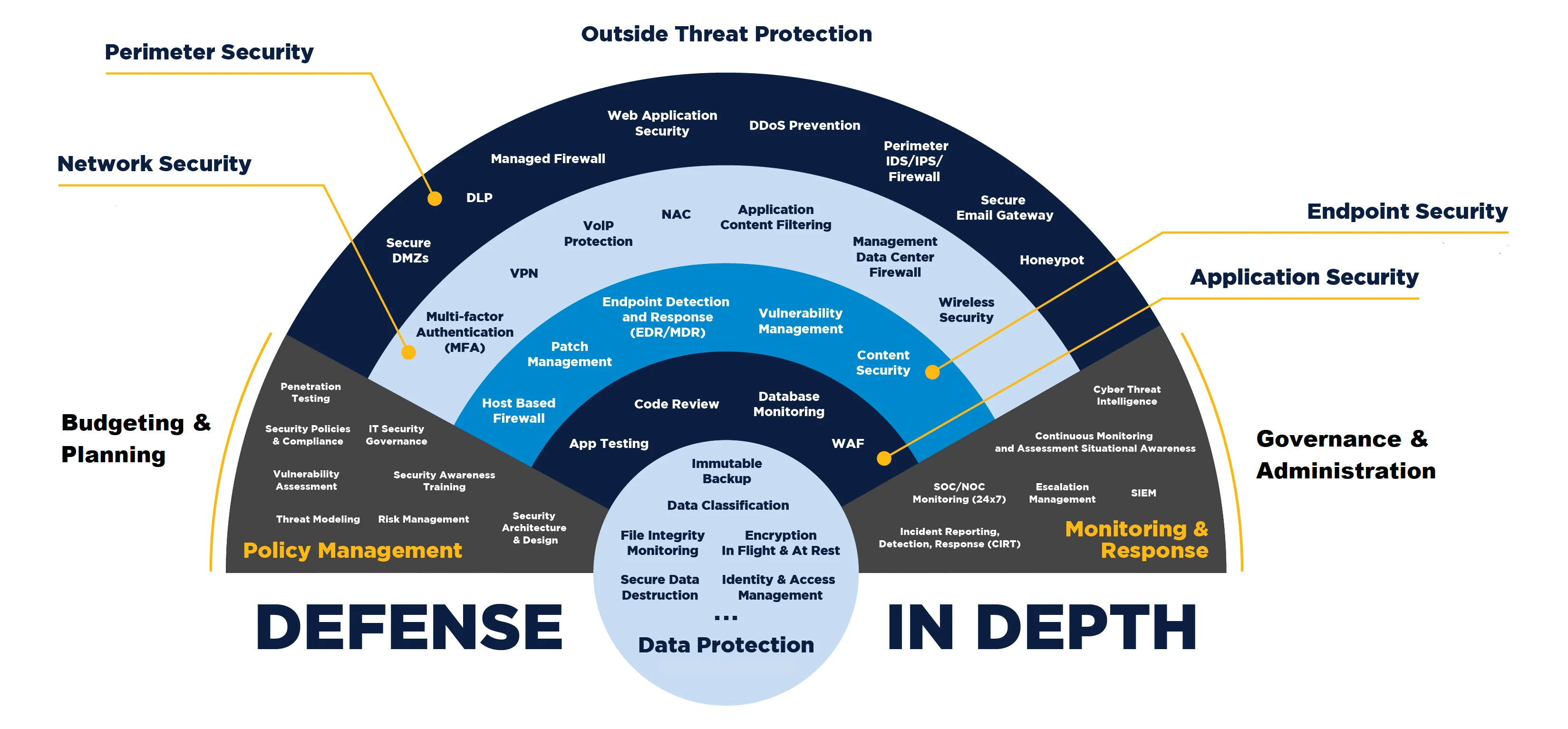
At HelioTech, we specialize in building robust system security architectures that protect your organization from evolving cyber threats. Our approach leverages the Defense-in-Depth (DiD) strategy, ensuring multiple layers of security controls are implemented across your IT infrastructure. By integrating network, cloud, and application security with industry standard frameworks, we create a resilient security posture that mitigates risks at every level.
Our Defense In Depth Approach
Defense-in-Depth involves deploying overlapping security measures so that if one layer fails, others remain intact. Our methodology includes:
By layering defenses, we ensure that attackers face multiple barriers, reducing the likelihood of a successful breach.
Key Components of Our Security Architecture

Network Security
Protecting your network infrastructure is the first line of defense. We implement:
- Next-Generation Firewalls (NGFW) – Palo Alto Networks, Fortinet, Cisco Firepower
- Intrusion Detection/Prevention Systems (IDS/IPS) – Snort, Suricata, Darktrace
- Network Segmentation & Zero Trust – VMware NSX, Cisco ISE, Zscaler Private Access
- Secure Remote Access – VPNs, SASE solutions (Cato Networks, Netskope)
These technologies prevent unauthorized access, detect anomalies, and enforce strict access policies.

Cloud Security
As businesses migrate to the cloud, securing cloud environments is critical. Our cloud security strategies include:
- Cloud Access Security Brokers (CASB) – Microsoft Defender for Cloud Apps, Netskope, McAfee MVISION
- Cloud Workload Protection (CWP) – Prisma Cloud (Palo Alto), AWS GuardDuty, Azure Security Center
- Identity & Access Management (IAM) – Okta, Microsoft Entra ID, Ping Identity
- Data Encryption & Key Management – AWS KMS, HashiCorp Vault, Thales CipherTrust
We ensure compliance with shared responsibility models while hardening cloud deployments against misconfigurations and breaches.

Application Security
Modern applications require protection at every stage of development and deployment. Our approach includes:
- Web Application Firewalls (WAF) – Cloudflare, Akamai, F5 BIG-IP
- Static & Dynamic Application Security Testing (SAST/DAST) – Checkmarx, Veracode, Burp Suite
- Runtime Application Self-Protection (RASP) – Imperva, Contrast Security
- API Security – Noname Security, Salt Security, Apigee
From secure coding practices to real-time threat mitigation, we safeguard applications against exploits like SQLi, XSS, and DDoS attacks.
Alignment With Cybersecurity Frameworks
Our security architectures are tailor made to meet our clients’ requirements and align with the appropriate Cybersecurity Framework (CSF) based on their industry and operations, ensuring compliance and best practices across all core functions.
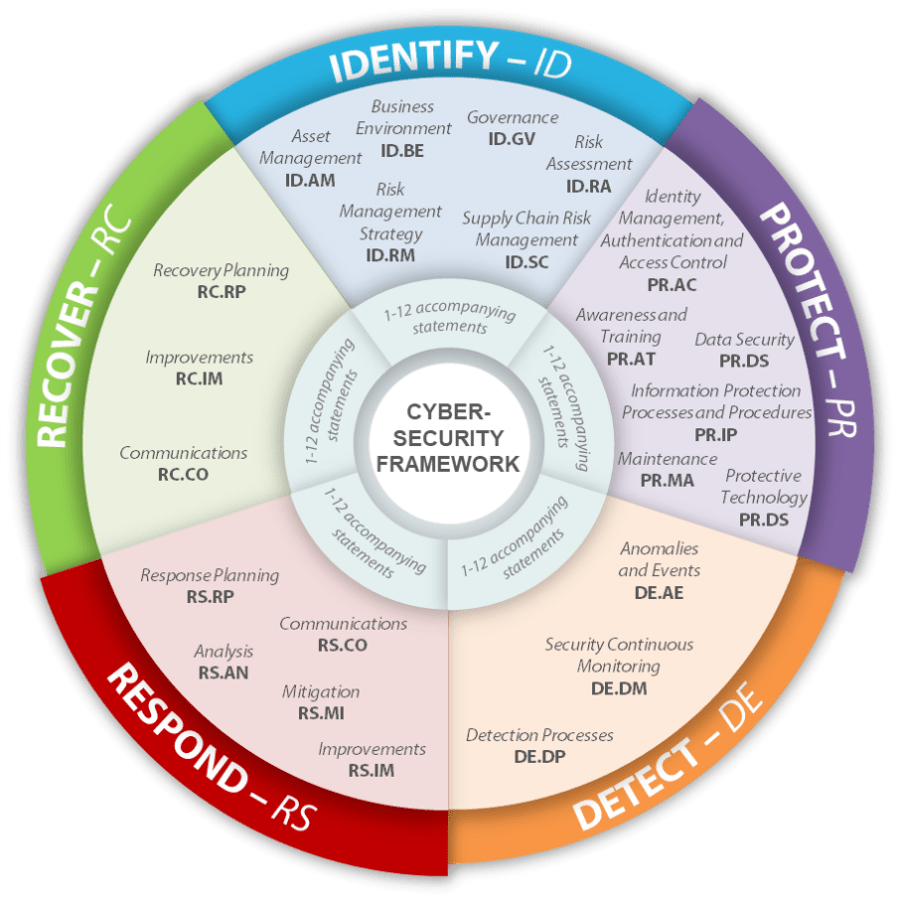
By mapping our security controls to specific security frameworks, we provide measurable, standards-based protection.
Why Choose HelioTech
- Comprehensive Protection: We cover all aspects of your system security, from network to cloud to applications.
- Custom Solutions: Our architectures are designed to fit your specific business needs.
- Proactive Defense: We stay ahead of emerging threats, ensuring your systems remain secure. Trust HelioTech to build a secure architecture that underpins your business operations.
- Proven Expertise: Certified security architects with deep knowledge of enterprise threats.
- Vendor-Agnostic Solutions: We select the best tools for your needs, not tied to a single provider.
- End-to-End Protection: From network perimeters to cloud workloads, we cover all attack surfaces.
- Regulatory Compliance: Aligned with NIST, ISO 27001, SOC 2, GDPR, PCI-DSS, HIPPA and more.
Contact our specialists for a system security architecture assessment today.
