Enterprise Security Assessment Services: Your Shield Against Cyber Threats
Uncover Hidden Vulnerabilities Before Attackers Do
In an era where cyberattacks occur every 39 seconds, proactive security assessments aren’t optional—they’re essential for survival. Our Enterprise Security Assessment Services deliver military-grade protection for your digital assets through a meticulous three-tier approach: discovery, validation, and proactive defense.
HelioTech's Battle-Tested Security Assessment Process
Intelligent Threat Mapping (Discovery Phase)
Effectively identify the scope of work
We begin by building your cyber threat profile:
- Asset inventory using Lansweeper and ServiceNow
- Attack surface mapping with InsightVM and Intruder.io
- Compliance gap analysis against 27+ regulatory frameworks
“We discovered 68% of clients had shadow IT assets they didn’t know existed until our assessment.” — Chief Security Architect
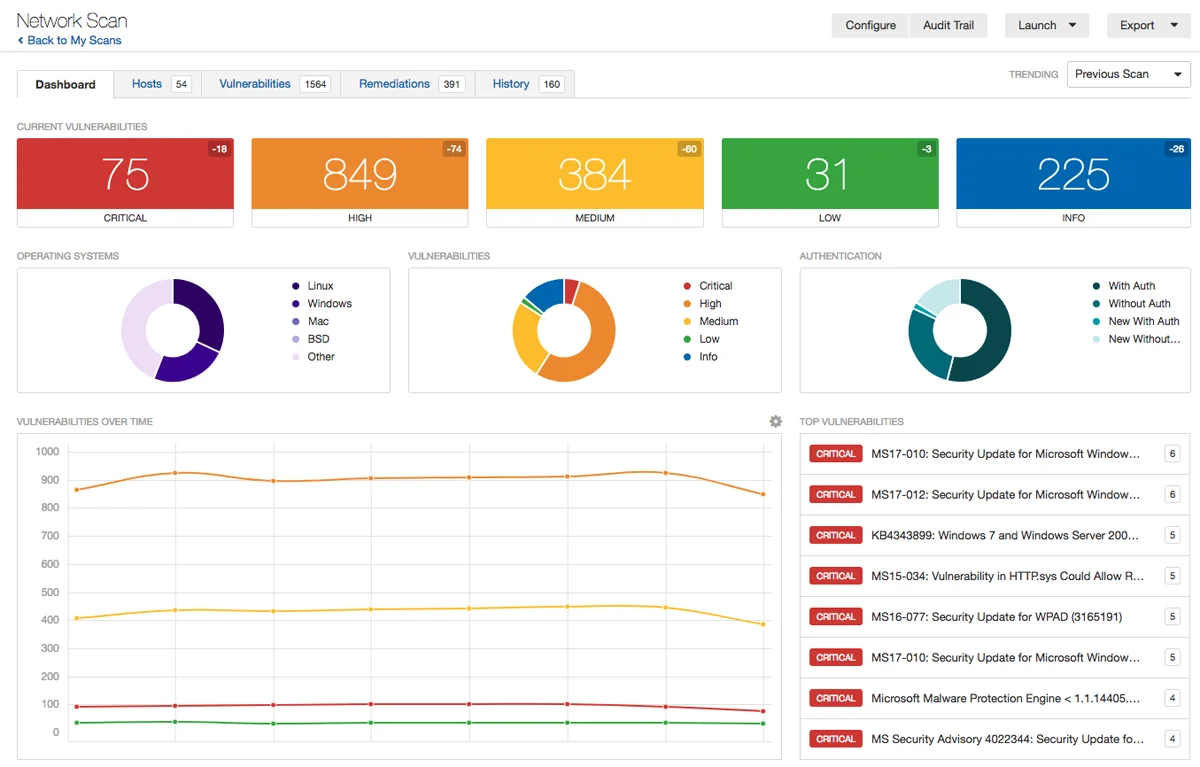
Precision Vulnerability Validation (Testing Phase)
Ensure that all known threats are mitigated
Automated Scanning Suite:
- Network: Tenable.io, Rapid7 InsightAppSec
- Cloud: Orca Security, Wiz.io
- Containers: Twistlock, Aqua Security
Human-Led Penetration Testing:
- Red team exercises using Cobalt Strike
- Physical security bypass testing
- Custom malware development simulations
API & Microservices Testing:
- Postman for API endpoint discovery
- Kiterunner for API brute force attacks
- GitLeaks for secret exposure detection
Active Threat Neutralization (Hunting Phase)
Proactively mitigate potential threats before they become exploits
Our elite hunters use MITRE ATT&CK framework to:
- Detect living-off-the-land binaries
- Uncover fileless malware
- Map adversary tradecraft patterns
Hunting Arsenal:
- Velociraptor for forensic collection
- Elastic Security for behavioral analytics
- BloodHound for Active Directory attack path visualization
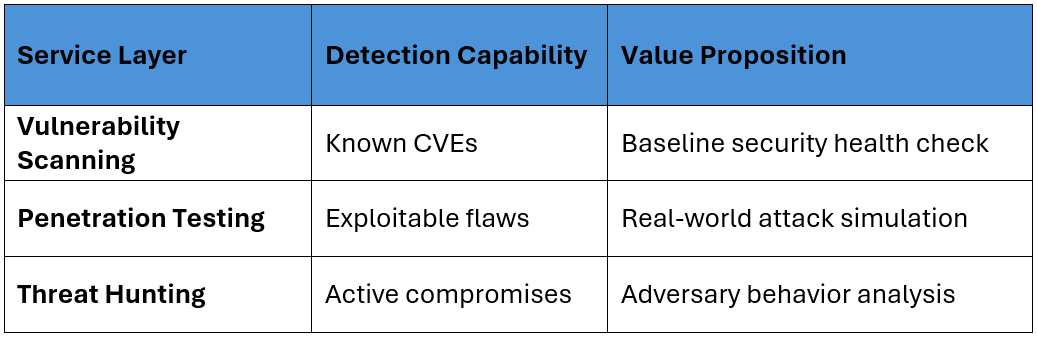
The Security Assessment Trifecta
Cutting-Edge Tools Driving Results
Combining experienced competency with effective tools ensures the best chance for success.
Why Global Enterprises Choose HelioTech
-Zero-Day Research Team developing custom exploits
-65% Faster Remediation through our SmartFix automation
-Military-Grade Reporting with VR attack visualizations
-24/7 Cyber SWAT Team for critical incidents
Recent Client Impact:
- Prevented $8.7M ransomware attack for healthcare provider
- Reduced critical vulnerabilities by 92% for financial institution
- Achieved FedRAMP compliance in record 11 weeks
Expert Answers to Critical Questions
Q: How do you handle zero-day vulnerabilities?
Q: What about IoT/OT environments?
Q: Can you test our third-party vendors?
Take Command of Your Security Posture
The average cost of a data breach is now $4.45 million. Our assessments pay for themselves by preventing just one incident.
Next Steps:
- Download Sample Report
- Schedule Technical Demo
- Speak to CISO Advisory Team
48-Hour Rapid Assessment Available for Emergency Situations