Building Trust Through Verified Cybersecurity Compliance
Operate with Confidence & Navigate with Ease

In today’s threat landscape, organizations need more than just security tools – they need verified proof of their cybersecurity posture. Our Information Assurance Certification & Accreditation (C&A) services provide the structured framework to validate your security controls, certify system integrity, and achieve formal authorization to operate.
We specialize in guiding organizations through the complete certification and accreditation lifecycle, ensuring compliance with:
- NIST Risk Management Framework (RMF)
- ISO 27001 certification requirements
- DoD DIACAP/DoD RMF processes
- FedRAMP authorization
- Industry-specific security standards
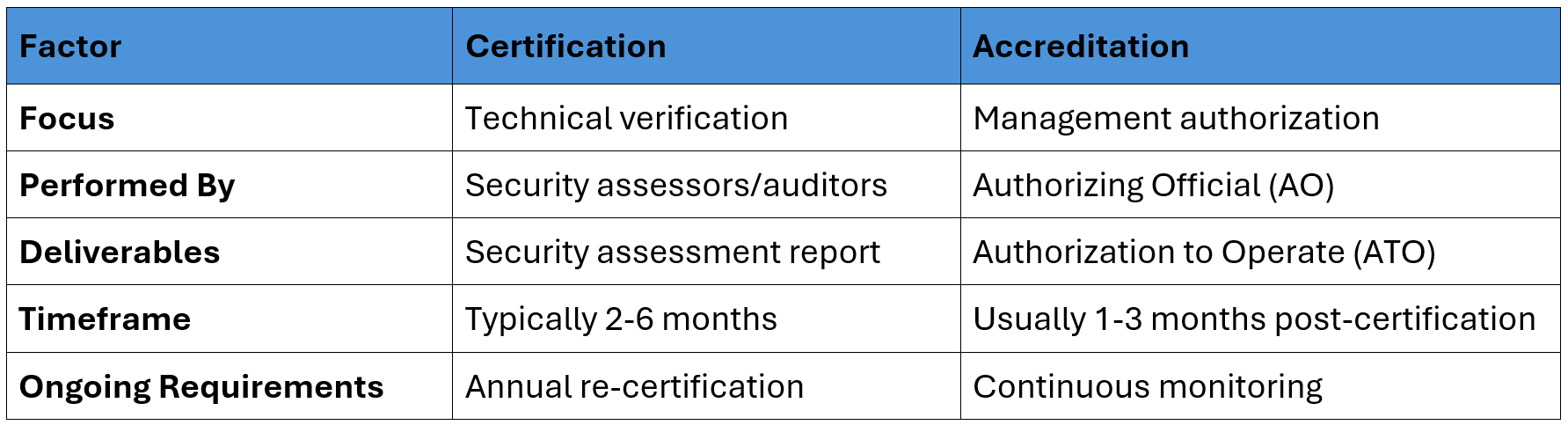
Understanding the C&A Lifecycle: Certification vs. Accreditation
Certification: The Technical Validation Process
Focused on verifying security controls meet defined standards
Our certification services involve:
- System Characterization
- Documenting system boundaries, components, and data flows
- Tools: Lucidchart, Microsoft Visio, Cameo Systems Modeler
- Security Control Assessment
- Technical testing of implemented safeguards
- Tools: Nessus, Qualys, Burp Suite, OpenSCAP
- Vulnerability Analysis
- Identifying gaps against baseline requirements
- Tools: Tenable.io, Rapid7 InsightVM, Wiz
- Risk Determination
- Evaluating residual risk levels
- Tools: RiskLens, FAIR Tool, Archer IRM
Accreditation: The Authorization Decision
The formal management approval to operate
Our accreditation services include:
- Documentation Package Preparation
- Compiling System Security Plans (SSP), POA&Ms, and test results
- Tools: eMASS, Xacta, RSA Archer
- Review Board Coordination
- Facilitating discussions with Authorizing Officials (AOs)
- Tools: GRC platforms with workflow automation
- Authorization to Operate (ATO) Issuance
- Managing conditional/interim/full ATO processes
- Maintaining continuous monitoring requirements
Our End-to-End C&A Methodology
We have developed a strategic process with proven capability maturity:
Phase 1: Pre-Assessment & Planning
- Conduct gap analysis against target framework
- Develop roadmap for control implementation
- Tool Example: CSAM for FedRAMP readiness assessments
Phase 2: Control Implementation & Testing
- Configure technical security controls
- Perform vulnerability scans and penetration tests
- Tool Example: Nessus for configuration compliance scanning
Phase 3: Certification Documentation
- Prepare System Security Plan (SSP)
- Document assessment procedures and results
- Tool Example: Telos Xacta for document automation
Phase 4: Accreditation Package Submission
- Compile complete evidence package
- Present to Authorizing Official (AO)
- Tool Example: CyberAB for FedRAMP package reviews
Phase 5: Continuous Monitoring
- Implement ongoing assessment activities
- Maintain authority to operate status
- Tool Example: Splunk for continuous monitoring alerts
Key Differences: Certification vs. Accreditation
Industry-Specific C&A Solutions
Why Choose HelioTech C&A Services?
- Former Assessors & Authorizing Officials on staff
- Framework-Specific Expertise across government and commercial standards
- Automated Documentation to accelerate timelines
- ATO Success Guarantee with remediation support